Key Takeaways
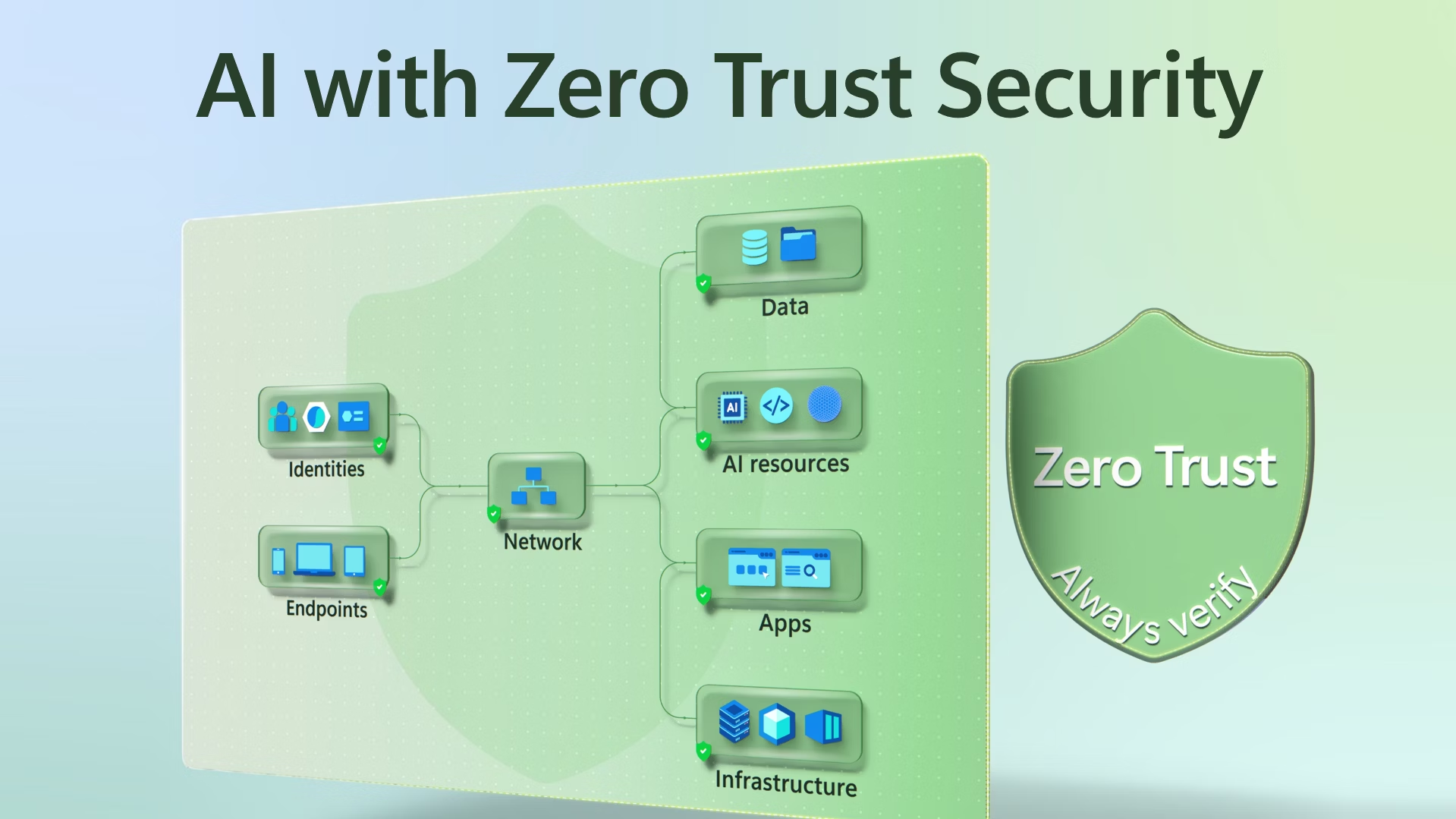
- Zero Trust applies the principle of “never trust, always verify,” meaning every access request is continuously authenticated and authorized.
- Techniques such as microsegmentation, continuous monitoring, and precise access management are crucial to a functional Zero Trust strategy.
- Organizations benefit from a reduced attack surface and minimized risk of lateral movement by attackers when implementing Zero Trust.
Table of Contents
- Understanding Zero Trust
- Core Principles of Zero Trust
- Implementing Zero Trust in Enterprise Networks
- Benefits of Zero Trust Adoption
- Challenges and Considerations
- Real-World Examples of Zero Trust Implementation
- Future Trends in Zero Trust Security
- Conclusion
As digital infrastructure expands and cyber threats become more sophisticated, traditional perimeter-based network security models are failing to provide adequate protection for enterprises. Instead, organizations are shifting towards robust frameworks like Zero Trust, which assume that no entity, whether internal or external, should ever be automatically trusted. The core strategy of this approach is to authenticate and verify every access attempt. Within this context, organizations are also exploring solutions such as cybersecurity SASE to enhance secure connectivity and fully realize the potential of Zero Trust architectures.
This article explores the underlying principles, implementation approach, advantages, and emerging trends surrounding the Zero Trust security model. With the rise of remote work and cloud adoption, maintaining a proactive, resilient security posture is more crucial than ever.
Understanding Zero Trust
Zero Trust is a modern security paradigm anchored in the principle that organizations can no longer rely on traditional trust boundaries, such as firewalls or secure perimeters. Instead, Zero Trust assumes that threats may exist both inside and outside the network at any given time, requiring continual verification of every request to access resources. This error responds to the limitations of legacy models, especially as mobile devices, cloud services, and remote users accelerate the blurring of network edges.
The growing frequency of security incidents, such as ransomware attacks and insider threats, necessitates a proactive approach in which all users and devices are treated as untrusted by default. Fundamental to Zero Trust is the idea of scrutinizing every access attempt, leveraging real-time data, user identity, context, and the health of the access request before granting access.
Core Principles of Zero Trust
- Continuous Verification: Every access request, whether initiated from an employee workstation or a third-party partner’s device, is evaluated and validated using available data on user roles, device health, and location.
- Least Privilege Access: Users and systems are only granted the minimum level of access necessary to perform their functions, reducing exposure to potential threats and error.
- Microsegmentation: The network is divided into isolated zones, so sensitive resources remain protected even if other segments are compromised. This minimizes the risk of lateral movement by attackers.
- Assume Breach: Security defenses are designed with the expectation that breaches will occur. Organizations prepare to detect, contain, and remediate threats quickly, reducing the impact.
Implementing Zero Trust in Enterprise Networks
- Identify Sensitive Data and Assets: Start by cataloging mission-critical data, applications, and resources, and identify what requires the most protection.
- Map Transaction Flows: Analyze how data flows across your environment to pinpoint vulnerable points and high-value assets.
- Enforce Access Controls: Apply dynamic policies based on user identity, device status, time, and location to ensure only entitled access is granted.
- Monitor and Analyze: Continuously observe and log network activity using tools that provide visibility into both routine and anomalous behavior.
- Automate Security Responses: Integrate automation to enforce rules and rapidly respond to detected threats before attackers can move laterally or escalate their activities.
Benefits of Zero Trust Adoption
- Enhanced Security Posture: Zero Trust’s rigorous access checks and real-time monitoring significantly reduce unauthorized access and prevent data breaches.
- Reduced Attack Surface: Microsegmentation, combined with least-privilege access policies, denies attackers easy network traversal.
- Improved Compliance: The visibility, controls, and logging inherent to Zero Trust architectures help organizations meet requirements laid out by frameworks such as GDPR and HIPAA.
- Support for Remote and Hybrid Work: Zero Trust’s adaptable architecture provides secure access for employees regardless of location, bypassing traditional VPN-related bottlenecks.
Challenges and Considerations
- Complexity: Shifting to a Zero Trust model requires detailed mapping of assets, users, and data flows, a process that can be challenging in large or rapidly evolving networks.
- Resource Allocation: Organizations often need to invest in new technologies and upskill security teams to deploy Zero Trust solutions across their infrastructure fully.
- User Experience: If not carefully managed, continuous authentication and strict access controls can introduce friction or slow productivity for legitimate users. It is important to balance security with usability.
Real-World Examples of Zero Trust Implementation
- Google’s BeyondCorp: Google developed the BeyondCorp framework, which brings Zero Trust principles to life by removing the distinction between internal and external networks and shifting dynamic access decisions to device and user identity. Employees can securely work from any location while maintaining strong protection for company resources.
- Department of Defense (DoD): The U.S. Department of Defense is deploying Zero Trust strategies across its networks to mitigate sophisticated threats and support warfighter safety. Their ambitious goal is to implement complete Zero Trust by 2027, with a focus on resilience and containment.
Future Trends in Zero Trust Security
- Artificial Intelligence (AI): Enterprise adoption of AI-driven tools enables teams to spot anomalies as they emerge, enabling them to act with unprecedented speed.
- Quantum Computing: Research efforts are underway to integrate quantum-safe security protocols into Zero Trust frameworks, preparing organizations for the unpredictable landscape of quantum-powered attacks. See this research on the quantum-driven Zero Trust framework for more details.
- Integration with 5G Networks: The roll-out of 5G presents expanded attack surfaces, and Zero Trust models are evolving to protect these new environments with context-aware access restrictions and next-generation endpoint controls.
Conclusion
Zero Trust is redefining enterprise security standards by discarding the assumption of trust and enforcing rigorous, continuous verification for every user and device. Organizations that embrace this approach benefit from stronger protection against data breaches, insider threats, and advanced cyber attacks. Implementing Zero Trust is undoubtedly a journey that requires effort and investment, but the evolving threat landscape and the demands of remote connectivity make it a critical pillar for future-proofing enterprise security.